This page will attempt to describe how to encrypt sensitive information contained in .NET config files using the RSA Key Container, as well as how to export/import the key from that container so that other developers may use the same key to work on the same project.
Helpful Tips: The aspnet_regiis.exe utility must be run as a administrator, otherwise you may receive “duplicate object” errors. In addition, you will want to run Visual Studio as an administrator to ensure the program has access to the RSA Key Container store.
Creating a Custom RSA Key Container
In this part we will create an RSA key container by using aspnet_regiis.exe with the -pc option. This identifies the RSA key container as a user-level key container. RSA key containers must be identified as either user-level (by using the -pku option) or machine-level (by not using the -pku option). For more information about machine-level and user-level RSA key containers, see Understanding Machine-Level and User-Level RSA Key Containers.
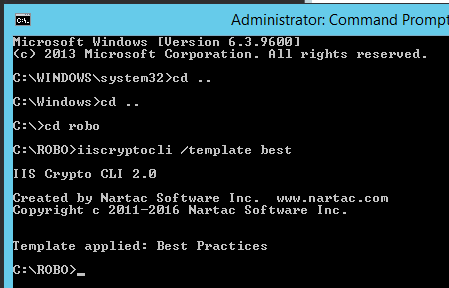
In this example the following command will create an RSA key container named SampleKeys that is a machine-level key container and is exportable:
cd \WINDOWS\Microsoft.Net\Framework\v4.0.*
aspnet_regiis -pc "SampleKeys"–exp
Adding your provider to the web.config
The following example shows the configProtectedData section of a Web.config file. The section specifies an RsaProtectedConfigurationProvider that uses a machine-level RSA key container named SampleKeys.
<configProtectedData>
<providers>
<add keyContainerName="SampleKeys" useMachineContainer="true" description="RsaCryptoServiceProvider" name="SampleKeys" type="System.Configuration.RsaProtectedConfigurationProvider,System.Configuration, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" />
</providers>
</configProtectedData>
Importing and Exporting the Key Container
In order for another developer to run your project (encrypted by your key) you will need to export a key to be used by another developer:
aspnet_regiis -px "SampleKeys" "C:\keys.xml" -pri
Once you pass this along to another user to use then import with the following command:
aspnet_regiis -pi "SampleKeys" "C:\keys.xml"
If this is a machine level container, the code should now run without the need to assign permissions. However, if it’s a user container (i.e. your app pool is ran by a specific user or service account), additional permissions may need to be assigned:
aspnet_regiis -pa "SampleKeys" "NT AUTHORITY\NETWORK SERVICE"
aspnet_regiis -pa "SampleKeys" "[impersonation account]"
To use the default RsaProtectedConfigurationProvider specified in the machine configuration, you must first grant the application’s Windows identity access to the machine key container named NetFrameworkConfigurationKey, which is the key container specified for the default provider. For example, the following command grants the NETWORK SERVICE account access to the RSA key container used by the default RsaProtectedConfigurationProvider:
aspnet_regiis -pa "NetFrameworkConfigurationKey" "NT AUTHORITY\NETWORK SERVICE"
Encrypting and Decrypting Config Sections
.NET allows specific sections of a config file to be encrypted, so non-sensitive information can still be accessed. To encrypt a section:
aspnet_regiis -pef [section] [path] -prov [provider]
Where [section] is the name of the config section, relative to the configuration tag. [path] is the relative path to the directory containing the web.config file. For example, the following commands will encrypt the appSettings section as well as the impersonation credentials:
cd C:\SolutionFolder
aspnet_regiis -pef appSettings ProjectFolder -prov SampleKeys
aspnet_regiis -pef system.web/identity ProjectFolder -prov SampleKeys
To decrypt the appSettings section:
aspnet_regiis -pdf appSettings ProjectFolder
Partially Encrypting a Section
It may be necessary to only encrypt part of a section in a web.config file. For example, if the appSettings section contains multiple, non-sensitive keys and only a subset contain sensitive information. To encrypt only a few keys, a second appSettings section must be created and the new keys moved into it. The keys are accessed exactly the same way in the code, so no coding changes are needed.
First, register a new section name called secureAppSettings by placing the following XML under the configuration node:
<configSections>
<section name="secureAppSettings" type="System.Configuration.NameValueSectionHandler, System, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" />
</configSections>
Next, create a new section called secureAppSettings and move the sensitive keys under it:
<secureAppSettings>
<add key="Username" value="XXX" />
<add key="Password" value="XXX" />
</secureAppSettings>
<appSettings>
<add key="NotSensitive" value="XXX" />
</appSettings>
Finally, the new secure section can be encrypted and decrypted independently of the existing appSettings section:
aspnet_regiis -pef secureAppSettings ProjectFolder -prov ProviderName
App.config
This Microsoft utility was designed for web.config files. It will not find app.config files for other project types. To encrypt these config files, just rename them to web.config prior to encrypting, then rename back afterwards.
Other Helpful Links: