- Get up to date on the APIs you need for users @ https://developer.box.com/v2.0/reference
- Sign up for your developer account at your enterprise @ https://yourenterprise.app.box.com/developers/console (replace with your enterprise application name in the link above)
- Create your Box app & API Key – link here and here
- Pull down the Box Windows SDK @ – https://github.com/box/box-windows-sdk-v2
- Update the pem file with your actual pem information from the app you created
- in case you’re wondering it should contain the —–BEGIN ENCRYPTED PRIVATE KEY—– and —–END ENCRYPTED PRIVATE KEY—–
- Update the properties appropriately in the app.config
<appSettings>
<add key="boxClientId" value="uniquestringhere" />
<add key="boxClientSecret" value="uniquestringheretoo" />
<add key="boxEnterpriseId" value="1234567" />
<add key="boxPrivateKeyPassword" value="uniquestringhereforpassword" />
<add key="boxPublicKeyId" value="uniquepublickeyid" />
<add key="ClientSettingsProvider.ServiceUri" value="useifneeded" />
</appSettings>
- From there you can update your Main runner in the program.cs appropriately. In the case of my sample below I am getting authorized, retrieving my users and looping through everyone but the main admin account and making them read-only. I’m also writing the information out to a file so I’ll have the logs of who was set / not set.
var privateKey = File.ReadAllText("private_key.pem");
var boxConfig = new BoxConfig(CLIENT_ID, CLIENT_SECRET, ENTERPRISE_ID, privateKey, JWT_PRIVATE_KEY_PASSWORD, JWT_PUBLIC_KEY_ID);
var boxJWT = new BoxJWTAuth(boxConfig);
var adminToken = boxJWT.AdminToken();
Console.WriteLine("Admin Token: " + adminToken);
Console.WriteLine();
var adminClient = boxJWT.AdminClient(adminToken);
var items = await adminClient.UsersManager.GetEnterpriseUsersAsync("", 0, 1000);
items.Entries.ForEach(async i =>
{
if (i.Login != "myspecialadminaccount@domain.com")
{
BoxUserRequest userRequest = new BoxUserRequest()
{
Id = i.Id,
Status = "cannot_delete_edit_upload"
};
System.Console.WriteLine("\t{0}", i.Name);
System.Console.WriteLine("\t{0}", i.Id);
System.Console.WriteLine("\t{0}", i.Login);
System.Console.WriteLine("\t{0}", i.Type);
System.Console.WriteLine(" ");
// Turn on for prod
BoxUser user = await adminClient.UsersManager.UpdateUserInformationAsync(userRequest);
Console.WriteLine(userRequest.Name + "updated to read-only");
System.Threading.Thread.Sleep(2000);
stringtext = i.Name.ToString() + " - " + i.Id.ToString() + " - " + i.Login.ToString() + " - " + i.Type.ToString() + " - updated to readonly" + Environment.NewLine;
System.Console.WriteLine(" ");
}
else
{
BoxUserRequest userRequest = new BoxUserRequest()
{
Id = i.Id
};
System.Console.WriteLine("\t{0}", i.Name);
System.Console.WriteLine("\t{0}", i.Id);
System.Console.WriteLine("\t{0}", i.Login);
System.Console.WriteLine("\t{0}", i.Type);
System.Console.WriteLine(" ");
Console.WriteLine(userRequest.Name + " NOT updated to read-only");
System.Threading.Thread.Sleep(2000);
stringtext = i.Name.ToString() + " - " + i.Id.ToString() + " - " + i.Login.ToString() + " - " + i.Type.ToString() + " - NOT updated to readonly" + Environment.NewLine;
System.Console.WriteLine(" ");
}
});
File.AppendAllText("C:\\Temp\\" + "log.txt", stringtext);
- Enable your box application to your enterprise accounts – link here
- Run your app (In TEST with test accounts! Then, with approval, prod.)
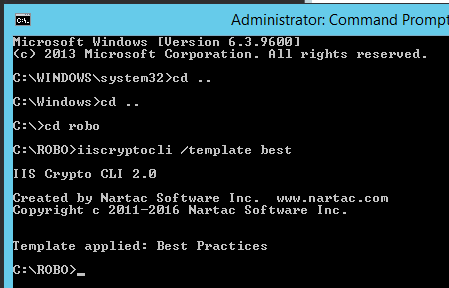
- If the app won’t run…check:
- code syntax errors
- certificate pem
- values in the app config
- authorization status in the admin Console on Box
- that your app is enabled and still available on the enterprise developer site
- If the app won’t run…check:
Hope this helps! I can send the source out on request if needed (just let me know).